|
|
|
|
Original Article
Cyber-Attack Detection System for Cyber-Physical Systems Using Machine Learning-Based Anomaly Detection
|
Dr. Harish Barapatre 1*, Harshal Patil 2, Anirudha Kamle 2, Vivek Singh 2 1 Associate Professor,
Department of Computer Engineering, Yadavrao
Tasgaonkar Institute of Engineering and Technology, Bhivpuri
Road Karjat, Maharashtra 410201, India 2 Student, Department of Computer
Engineering, Yadavrao Tasgaonkar Institute of
Engineering and Technology, Bhivpuri Road Karjat, Maharashtra 410201, India |
|
|
|
ABSTRACT |
||
|
Cyber-Physical Systems (CPS) are increasingly deployed in critical domains such as smart grids, industrial automation, healthcare, and transportation, where the integration of computational and physical components introduces significant security challenges. These systems are highly vulnerable to cyber-attacks such as false data injection, denial-of-service, and stealthy manipulation, which can lead to severe physical and economic consequences. Traditional security mechanisms are insufficient due to the dynamic and heterogeneous nature of CPS environments [1], [2]. This paper proposes a conceptual machine learning-based cyber-attack detection framework tailored for CPS environments. The framework focuses on real-time anomaly detection by analyzing multi-source data streams from sensors, network traffic, and control signals. A hybrid detection approach is designed that combines statistical feature analysis and supervised learning models to identify deviations from normal system behavior. The proposed model introduces a risk scoring mechanism that evaluates system states based on behavioral inconsistencies, enabling early detection of potential threats. The framework emphasizes scalability, adaptability, and low-latency detection, which are critical for real-time CPS applications. Unlike conventional signature-based systems, the proposed approach is capable of detecting unknown and zero-day attacks. The study provides a structured design and mathematical formulation for anomaly scoring and decision-making processes, making it suitable for further implementation and validation in real-world CPS scenarios [3]. Keywords: Cyber-Physical Systems, Cyber Attack
Detection, Anomaly Detection, Machine Learning, Intrusion Detection, Smart
Systems |
||
INTRODUCTION
Cyber-Physical
Systems (CPS) represent a tightly coupled integration of computational
intelligence and physical processes, where sensors, actuators, communication
networks, and control algorithms operate in a coordinated manner. These systems
are widely deployed in critical infrastructures such as smart grids, industrial
control systems (ICS), autonomous transportation, and healthcare monitoring
systems. Due to their real-time nature and dependence on accurate data
exchange, CPS environments are highly sensitive to cyber-attacks that can
propagate from the cyber layer to the physical layer, causing serious
operational failures and safety risks [1].
In recent years,
the attack surface of CPS has expanded significantly due to increased
connectivity, use of IoT devices, and reliance on cloud-based control
mechanisms. Common attack types include False Data Injection Attacks (FDIA),
Denial of Service (DoS), replay attacks, and stealthy integrity attacks. These
attacks often remain undetected by traditional security mechanisms because they
are designed to mimic normal system behavior or
exploit system dynamics [2]. As a result, conventional rule-based and signature-based
intrusion detection systems are no longer sufficient for securing CPS
environments.
To address these
challenges, researchers have started exploring data-driven and machine
learning-based approaches for detecting anomalies in CPS. Machine learning
models can learn normal system behavior from
historical data and identify deviations that indicate potential cyber threats.
Techniques such as Support Vector Machines (SVM), Random Forests, Neural
Networks, and Deep Learning models have shown promising results in anomaly
detection tasks [3]. However, many existing solutions focus only on either network-level
anomalies or physical-layer inconsistencies, failing to provide a unified
detection mechanism across the entire CPS architecture.
Another limitation
of existing approaches is the lack of real-time adaptability and scalability.
CPS environments are dynamic, with changing system states, varying workloads,
and evolving attack strategies. Therefore, an effective detection system must be
capable of continuous learning, low-latency processing, and multi-source data
fusion. Additionally, there is a need for interpretable decision-making
mechanisms that can quantify the severity of detected anomalies and assist in
timely mitigation.
Motivated by these
challenges, this paper proposes a machine learning-based cyber-attack detection
framework specifically designed for CPS environments. The framework integrates
data from multiple layers, including sensor readings, control signals, and network
traffic, to perform comprehensive anomaly detection. A risk-based scoring
mechanism is introduced to evaluate system behavior
and detect abnormal conditions at an early stage. The proposed approach aims to
enhance detection accuracy, reduce false positives, and provide a scalable
solution suitable for real-time CPS applications.
The main
contributions of this work are as follows:
·
A
unified framework for cyber-attack detection across cyber and physical layers
of CPS
·
Integration
of multi-source data for improved anomaly detection
·
A risk
scoring model for quantifying system behavior
deviations
·
A
scalable and real-time detection approach suitable for dynamic CPS environments
Proceed to
Literature Review?
next
Literature
Review
Cyber-Physical
Systems (CPS) security has attracted significant research attention due to the
increasing number of cyber-attacks targeting critical infrastructures. Various
approaches have been proposed for intrusion detection and anomaly detection in
CPS, ranging from traditional rule-based systems to advanced machine learning
and deep learning techniques.
Early approaches
to CPS security primarily relied on signature-based intrusion detection systems
(IDS), which detect known attack patterns using predefined rules. While
effective for previously identified threats, these systems fail to detect
zero-day attacks and adaptive adversaries [4]. To overcome this limitation,
anomaly-based detection methods were introduced, where the system learns normal
behavior and flags deviations as potential attacks.
Machine learning
techniques have been widely explored for anomaly detection in CPS. For example,
Support Vector Machines (SVM) and k-Nearest Neighbors
(k-NN) have been used to classify normal and abnormal system states based on
feature vectors derived from sensor and network data [5]. Random Forest and
Decision Tree models provide improved interpretability and have been applied in
industrial control systems for detecting anomalies in operational data [6].
However, these models often require careful feature engineering and may
struggle with high-dimensional CPS data.
Deep
learning-based approaches have further improved detection capabilities.
Recurrent Neural Networks (RNN) and Long Short-Term Memory (LSTM) networks are
particularly effective in modeling temporal
dependencies in CPS data streams [7]. These models can detect subtle anomalies
in time-series data, making them suitable for applications such as smart grids
and autonomous systems. Convolutional Neural Networks (CNN) have also been
applied for feature extraction from multidimensional CPS data [8]. Despite their
effectiveness, deep learning models often require large datasets, high
computational resources, and lack interpretability.
Another line of
research focuses on physics-based and hybrid models that combine system
dynamics with data-driven techniques. These approaches leverage knowledge of
physical processes to improve detection accuracy and reduce false positives
[9]. For instance, state estimation techniques and Kalman filters have been
used to detect false data injection attacks in power systems. However, purely
physics-based models may fail when system dynamics are highly complex or
partially unknown.
Recent studies
have proposed hybrid frameworks that integrate multiple data sources, including
sensor readings, control signals, and network traffic. Such multi-layer
detection systems provide better visibility into CPS behavior
and improve detection performance [10]. However, many of these frameworks lack
a unified risk evaluation mechanism and are not optimized for real-time
deployment.
The following
table summarizes key existing works and their limitations:
|
Paper |
Method |
Limitation |
|
[4] |
Signature-based IDS |
Cannot detect unknown attacks |
|
[5] |
SVM, k-NN |
Limited scalability, feature dependency |
|
[6] |
Random Forest |
Requires feature engineering |
|
[7] |
LSTM-based detection |
High computational cost |
|
[8] |
CNN-based models |
Needs large datasets |
|
[9] |
Physics-based models |
Limited adaptability |
|
[10] |
Hybrid CPS frameworks |
Lack real-time risk scoring |
From the
literature, it is evident that although significant progress has been made,
there is still a need for a unified, scalable, and real-time cyber-attack
detection framework that integrates multi-source data and provides
interpretable decision-making.
Proceed to
Research Gap?
next
Research
Gap and Problem Statement
Despite
significant advancements in cyber-attack detection techniques for
Cyber-Physical Systems (CPS), several critical limitations still exist in
current research and practical implementations. These limitations create gaps
that must be addressed to ensure reliable and real-time protection of CPS
environments.
One of the primary
gaps identified from the literature is the lack of unified detection across
cyber and physical layers. Most existing approaches focus either on
network-level anomalies or physical process deviations, but not both
simultaneously. This separation reduces the overall effectiveness of detection
systems, especially in coordinated attacks where adversaries manipulate both
data and system dynamics.
Another major gap
is the absence of real-time and scalable detection mechanisms. Many machine
learning and deep learning models proposed in literature are computationally
intensive and not optimized for low-latency environments. Since CPS
applications such as smart grids and industrial automation require immediate
response, delayed detection can lead to severe consequences.
Additionally,
current systems lack an effective risk quantification mechanism. Most anomaly
detection models simply classify behavior as normal
or abnormal without providing a severity score. This binary decision-making is
insufficient in real-world scenarios where prioritization of threats is
essential for timely mitigation.
There is also a
limitation in multi-source data integration. CPS generates heterogeneous data
from sensors, actuators, control signals, and network logs. Existing models
often process these data sources independently, which leads to incomplete
understanding of system behavior and increases the
chances of false positives or missed detections.
Another important
challenge is adaptability to dynamic environments. CPS conditions continuously
change due to varying workloads, environmental factors, and system updates.
Many traditional models are static and fail to adapt to new patterns, making
them vulnerable to evolving attack strategies.
Based on these
identified gaps, the core problem addressed in this paper can be defined as
follows:
There is a need to
design a unified, scalable, and real-time cyber-attack detection system for
Cyber-Physical Systems that can integrate multi-source data, accurately detect
both known and unknown attacks, and provide a quantitative risk-based decision
mechanism for effective threat identification and response.
To solve this
problem, this paper proposes a machine learning-based framework that combines
anomaly detection with a risk scoring model. The system is designed to operate
across both cyber and physical layers, process heterogeneous data streams, and
provide interpretable outputs for decision-making. The proposed approach aims
to enhance detection accuracy, reduce false alarms, and support real-time CPS
security requirements.
Proceed to
Proposed Framework?
next
Proposed
Cyber-Attack Detection Framework
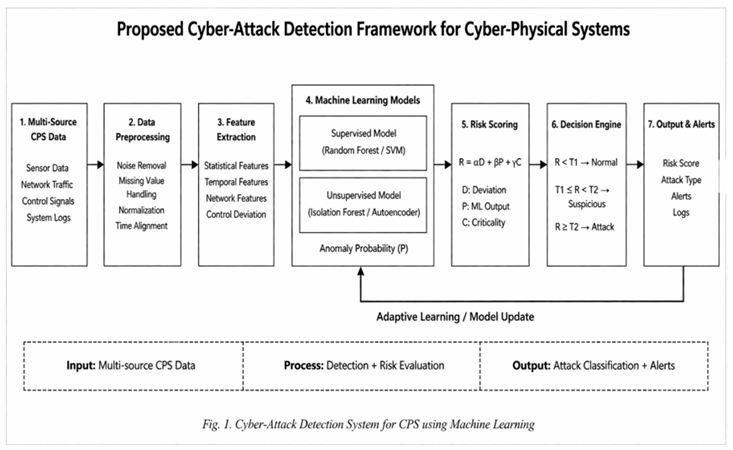
The proposed
system is designed as a unified, multi-layer cyber-attack detection framework
for Cyber-Physical Systems (CPS). The framework integrates data from both cyber
and physical components to detect anomalies and identify potential attacks in
real time. The overall architecture follows a structured pipeline that
processes input data, extracts meaningful features, applies machine learning
models, and generates a risk-based decision output.
|
Figure
1
|
|
Figure 1 Shows the Proposed
System Architecture. |
System
Overview
The system
operates in five major layers:
1)
Data
Acquisition Layer
2)
Preprocessing
and Feature Engineering Layer
3)
Detection
and Analysis Layer
4)
Risk
Scoring and Decision Layer
5)
Output
and Alert Layer
Each layer is
designed to handle a specific function in the detection pipeline, ensuring
modularity, scalability, and real-time performance.
1)
Data
Acquisition Layer
This layer
collects real-time data from multiple CPS components, including:
·
Sensor
data (temperature, pressure, voltage, etc.)
·
Actuator
signals (control commands)
·
Network
traffic (packets, latency, communication logs)
·
System
logs and events
The integration of
these heterogeneous data sources ensures a holistic view of system behavior across both cyber and physical domains.
2)
Preprocessing
and Feature Engineering Layer
Raw CPS data is
often noisy, incomplete, and heterogeneous. This layer performs:
·
Data
cleaning (removal of noise and missing values)
·
Normalization
and scaling
·
Time-series
alignment
·
Feature
extraction (statistical features, temporal features, network features)
Examples of
extracted features include mean, variance, packet rate, delay patterns, and
control signal deviations. These features help the model understand both normal
and abnormal system behavior.
3)
Detection
and Analysis Layer
This is the core
intelligence layer of the system. It applies machine learning models to detect
anomalies. The system can use:
·
Supervised
models (e.g., Random Forest, SVM) for known attack patterns
·
Unsupervised
models (e.g., Isolation Forest, Autoencoders) for unknown anomalies
A hybrid approach
is used where both models work together to improve detection accuracy. The
output of this layer is an anomaly indicator for each data instance.
4)
Risk
Scoring and Decision Layer
Instead of binary
classification (normal/attack), the system computes a risk score based on
multiple factors:
·
Degree
of deviation from normal behavior
·
Frequency
of anomalies
·
Importance
of affected system component
This layer
aggregates outputs from detection models and assigns a severity score to each
event. Based on predefined thresholds, the system decides whether the activity
is:
·
Normal
·
Suspicious
·
Critical
Attack
This approach
improves interpretability and helps prioritize responses.
5)
Output
and Alert Layer
The final layer
generates:
·
Real-time
alerts for detected attacks
·
Risk
scores and severity levels
·
Visualization
dashboards for monitoring
Alerts can be sent
to system administrators or automated response systems for immediate action.
System Flow
Input
(Multi-source CPS Data)
·
Data
Preprocessing
·
Feature
Extraction
·
Machine
Learning Detection
·
Risk
Scoring
·
Decision
Making
·
Alert
Generation
Input–Process–Output
Mapping
Input:
Multi-source CPS
data (sensor, network, control signals)
Process:
Preprocessing
→ Feature Engineering → ML-based Detection → Risk Evaluation
Output:
Anomaly detection
results + Risk score + Attack classification + Alerts
Key Advantages of Proposed Framework
·
Unified
detection across cyber and physical layers
·
Capability
to detect both known and unknown attacks
·
Real-time
processing and scalability
·
Risk-based
decision-making instead of binary output
·
Modular
architecture for easy deployment and extension
This framework
provides a strong foundation for implementing an intelligent and adaptive
cyber-attack detection system in CPS environments.
Proceed to
Mathematical Model?
next
Mathematical Model
The proposed
cyber-attack detection system uses a risk-based anomaly scoring mechanism. The
mathematical model is designed to quantify abnormal behavior
in Cyber-Physical Systems (CPS) by combining multiple indicators such as
feature deviation, anomaly probability, and system criticality.
1)
Feature
Deviation Score
Display Format:
D = (1/n) Σ
|xi − μi|
Word Equation
Format:
D = \frac{1}{n}
\sum |x_i - \mu_i|
Where:
·
xi =
observed feature value
·
μi =
expected (normal) value of feature
·
n =
total number of features
Explanation:
This equation
measures how much the current system state deviates from normal behavior. Higher deviation indicates abnormal activity.
2)
Anomaly
Probability Score
Display Format:
P = f(x)
Word Equation
Format:
P = f(x)
Where:
·
P =
probability of anomaly
·
f(x) =
machine learning model output (e.g., classifier or anomaly detector)
Explanation:
This represents
the likelihood that a given input belongs to an attack class. It is obtained
from models like SVM, Random Forest, or Neural Networks.
3)
Weighted
Risk Score
Display Format:
R = αD +
βP + γC
Word Equation
Format:
R = \alpha D +
\beta P + \gamma C
Where:
·
R =
overall risk score
·
D =
deviation score
·
P =
anomaly probability
·
C =
criticality of system component
·
α,
β, γ = weighting factors (α + β + γ = 1)
Explanation:
This is the core
equation of the system. It combines deviation, model prediction, and system
importance to generate a final risk score. The weights control the influence of
each component.
4)
Decision
Threshold Function
Display Format:
Attack = {
0, if R < T1
1, if T1 ≤ R
< T2
2, if R ≥ T2
}
Word Equation
Format:
Attack =
\begin{cases} 0, & R < T_1 \ 1, & T_1 \leq
R < T_2 \ 2, & R \geq T_2 \end{cases}
Where:
·
T1 =
lower threshold (normal vs suspicious)
·
T2 =
upper threshold (suspicious vs attack)
·
0 =
Normal
·
1 =
Suspicious
·
2 =
Critical Attack
Explanation:
This function
classifies system behavior into three levels based on
the computed risk score. It helps in prioritizing alerts and responses.
Overall Model Interpretation
The system first
calculates deviation from normal behavior, then
estimates anomaly probability using machine learning, and finally combines
these with system criticality to compute a risk score. Based on this score, the
system classifies the state into normal, suspicious, or attack.
This mathematical
formulation ensures:
·
Quantitative
decision-making
·
Improved
interpretability
·
Flexibility
to adjust system sensitivity
Proceed to
Algorithm?
next
Algorithm
The proposed
algorithm defines the step-by-step working of the cyber-attack detection system
in Cyber-Physical Systems (CPS). It integrates data preprocessing, anomaly
detection, and risk-based decision-making into a unified flow.
Algorithm:
Cyber-Attack Detection in CPS
Input:
·
Multi-source
CPS data stream X (sensor data, network data, control signals)
·
Trained
machine learning model f(x)
·
Normal
feature reference μ
·
System
criticality values C
·
Thresholds
T1, T2
·
Weights
α, β, γ
Output:
·
Attack
Classification (Normal / Suspicious / Critical)
·
Risk
Score R
·
Alert
Signal
Steps:
1)
Data
Collection
Collect real-time
data X from CPS components
2)
Data
Preprocessing
·
Clean
missing or noisy data
·
Normalize
feature values
·
Align
time-series data
3)
Feature
Extraction
·
Extract
features xi from input data
·
Construct
feature vector F = {x1, x2, ..., xn}
4)
Compute
Deviation Score
Use Eq. (1):
D = (1/n) Σ
|xi − μi|
5)
Compute
Anomaly Probability
Use Eq. (2):
P = f(x)
6)
Compute
Risk Score
Use Eq. (3):
R = αD +
βP + γC
7)
Decision
Making
Use Eq. (4):
If R < T1
→ Normal
If T1 ≤ R
< T2 → Suspicious
If R ≥ T2
→ Critical Attack
8)
Alert
Generation
If Suspicious
→ Generate warning
If Critical
→ Trigger immediate alert
9)
Logging
and Feedback
Store detected
events
Update model
periodically (optional adaptive learning)
Pseudocode Representation
Input: X, μ,
C, α, β, γ, T1, T2
Output: Attack_Label, Risk_Score
Begin
Collect data X
Preprocess X
Extract features F
Compute D = (1/n) * Σ |xi - μi|
Compute P = f(X)
Compute R = α*D + β*P + γ*C
If R < T1 then
Label = "Normal"
Else if R < T2 then
Label = "Suspicious"
Else
Label = "Critical Attack"
End If
Generate Alert based on Label
Store results
End
Algorithm Characteristics
·
Real-time
processing capability
·
Supports
both known and unknown attack detection
·
Modular
design for easy extension
·
Uses
quantitative risk scoring for better decision-making
This algorithm
ensures that the detection system is not only accurate but also interpretable
and scalable for CPS environments.
Proceed to
Methodology?
next
Methodology / Working
The proposed
cyber-attack detection system for Cyber-Physical Systems (CPS) follows a
structured end-to-end workflow that ensures reliable, real-time, and adaptive
detection of anomalies. Since this is a conceptual framework, the methodology
focuses on how the system would operate in a practical deployment scenario
without assuming any specific dataset.
Overall Working Pipeline
Input Data
·
Preprocessing
·
Feature
Engineering
·
Model-Based
Detection
·
Risk
Evaluation
·
Decision
Output
1)
Input
Data Collection
The system
continuously collects multi-source data from CPS components:
·
Physical
layer: sensor readings (temperature, voltage, pressure, etc.)
·
Control
layer: actuator signals and control commands
·
Cyber
layer: network traffic, packet flow, logs
This multi-layer
data acquisition ensures that both cyber and physical anomalies are captured.
2)
Data
Preprocessing
Before analysis,
raw data is processed to ensure quality and consistency:
·
Noise
removal using filtering techniques
·
Handling
missing values using interpolation or imputation
·
Normalization
to bring all features to a common scale
·
Time
synchronization for aligning sensor and network data
This step ensures
that the system operates on clean and consistent input data.
3)
Feature
Engineering
Relevant features
are extracted to represent system behavior
effectively. These include:
·
Statistical
features: mean, variance, standard deviation
·
Temporal
features: lag values, trends, rate of change
·
Network
features: packet rate, latency, protocol distribution
·
Control
deviation features: difference between expected and actual control signals
These features
form a structured feature vector used for detection.
4)
Model-Based
Detection
The system uses a
hybrid machine learning approach:
·
Supervised
Learning:
Detects known
attack patterns using trained classifiers such as Random Forest or SVM
·
Unsupervised
Learning:
Detects unknown
anomalies using models like Isolation Forest or Autoencoders
Both outputs are
combined to generate an anomaly probability score. This hybrid strategy
improves robustness against both known and unseen attacks.
5)
Risk
Evaluation Mechanism
Using the
mathematical model defined earlier:
·
Deviation
score (D) measures how far the system deviates from normal behavior
·
Probability
score (P) indicates likelihood of anomaly
·
Criticality
factor (C) reflects importance of affected component
These are combined
to compute a final risk score:
R = αD +
βP + γC
This step
transforms raw detection into an interpretable metric.
6)
Decision
Making
Based on the
computed risk score:
·
Low risk
→ Normal operation
·
Medium
risk → Suspicious activity
·
High
risk → Critical cyber-attack
Threshold-based
classification ensures clear decision boundaries.
7)
Alert
Generation and Response
The system
generates:
·
Real-time
alerts for suspicious and critical events
·
Severity-based
notifications
·
Logs for
further analysis
Optional
integration with automated response systems can trigger actions such as:
·
Blocking
network traffic
·
Isolating
affected components
·
Triggering
fail-safe mechanisms
8)
Continuous
Learning (Optional Extension)
To handle dynamic
CPS environments, the system can be extended with:
·
Online
learning for adapting to new patterns
·
Periodic
retraining using updated data
·
Feedback
loop from detected incidents
This ensures
long-term effectiveness and resilience.
Methodology Strengths
·
Handles
heterogeneous CPS data
·
Supports
real-time detection
·
Detects
both known and unknown attacks
·
Provides
interpretable risk-based output
·
Scalable
for large CPS environments
This methodology
ensures a practical and deployable approach for cyber-attack detection in CPS
systems.
Proceed to
Expected Results and Discussion?
next
Expected Results and Discussion
Since the proposed
system is a conceptual framework, the expected results are discussed based on
logical system behavior, design characteristics, and
comparison with existing approaches rather than experimental evaluation.
Expected
Outcomes
1)
Improved
Detection Capability
The integration of
multi-source data (sensor, network, and control signals) is expected to
significantly improve detection accuracy compared to single-layer systems. By
observing both cyber and physical behaviors
simultaneously, the system can detect complex and coordinated attacks such as
false data injection and stealth attacks more effectively.
2)
Detection
of Unknown Attacks
Unlike
signature-based systems, the use of unsupervised learning models enables the
detection of unknown and zero-day attacks. The anomaly detection component is
expected to identify deviations even when no prior attack pattern exists.
3)
Reduced
False Positives
The inclusion of a
risk scoring mechanism (combining deviation, probability, and criticality)
helps filter out minor fluctuations that are not actual attacks. This is
expected to reduce false alarms compared to traditional anomaly detection
systems that rely on single metrics.
4)
Real-Time
Performance
The modular
architecture and lightweight mathematical model are designed for low-latency
processing. Therefore, the system is expected to operate in near real-time,
making it suitable for critical CPS applications such as industrial automation
and smart grids.
5)
Interpretability
of Results
The risk score (R)
provides a quantitative and interpretable measure of system behavior.
Instead of a simple binary output, system administrators receive graded alerts
(Normal, Suspicious, Critical), which improves decision-making and response
prioritization.
Discussion
The proposed
framework addresses several limitations identified in existing literature.
First, it provides a unified detection mechanism across both cyber and physical
layers, which is essential for modern CPS environments. Second, the hybrid
machine learning approach enhances robustness by combining strengths of
supervised and unsupervised models.
The risk-based
decision mechanism plays a crucial role in improving system usability. In
real-world scenarios, not all anomalies require immediate action. By
categorizing events into multiple severity levels, the system allows operators
to prioritize responses effectively.
However, certain
challenges may arise during practical implementation:
·
Data
Heterogeneity: Integrating diverse data sources may require complex
preprocessing and synchronization
·
Model
Training: Supervised models require labeled data,
which may not always be available
·
Parameter
Tuning: Selection of weights (α, β, γ) and thresholds (T1, T2)
can impact system performance
·
Computational
Overhead: Real-time processing of large-scale CPS data may require optimization
Despite these
challenges, the proposed framework provides a strong foundation for developing
a scalable and intelligent cyber-attack detection system. It balances detection
accuracy, interpretability, and real-time performance, making it suitable for
practical CPS deployments.
Proceed to
Conclusion?
next
Conclusion and Future Scope
This paper
presented a conceptual machine learning-based cyber-attack detection framework
for Cyber-Physical Systems (CPS). The proposed system addresses critical
security challenges by integrating data from both cyber and physical layers,
enabling comprehensive monitoring and anomaly detection. Unlike traditional
approaches that rely on single-layer analysis or signature-based detection, the
proposed framework adopts a hybrid learning strategy combined with a risk-based
scoring mechanism to provide accurate and interpretable results.
The mathematical
model introduced in this work allows quantitative evaluation of system behavior by combining deviation analysis, anomaly
probability, and component criticality. This enables the system to classify
events into multiple severity levels rather than simple binary outputs,
improving decision-making and response prioritization. The modular architecture
ensures scalability and supports real-time detection, making it suitable for
dynamic CPS environments such as smart grids, industrial automation, and
intelligent transportation systems.
The study
highlights that integrating multi-source data and combining supervised and
unsupervised learning techniques can significantly enhance detection
performance while reducing false positives. Additionally, the inclusion of a
risk scoring mechanism improves the practical usability of the system by
providing actionable insights instead of raw anomaly outputs.
Future Scope
The proposed
framework can be extended in several directions to enhance its practical
applicability:
·
Integration
with real-world CPS datasets for experimental validation and performance
benchmarking
·
Implementation
of deep learning models such as LSTM or Graph Neural Networks for capturing
complex system dependencies
·
Development
of adaptive learning mechanisms for handling concept drift in dynamic
environments
·
Incorporation
of Explainable AI (XAI) techniques to improve transparency and trust in
decision-making
·
Deployment
on edge or fog computing platforms for ultra-low latency detection
·
Integration
with automated response systems for self-healing CPS environments
Overall, the
proposed system provides a strong foundation for building intelligent,
scalable, and real-time cyber-attack detection solutions for modern
Cyber-Physical Systems.
Proceed to
References?
next
ACKNOWLEDGMENTS
None.
REFERENCES
Abokifa,
A. A., Haddad, K., and Lo, C. S. (2019). Detection of Cyber Attacks on Water
Distribution Systems Using Machine Learning. Journal of Water Resources
Planning and Management, 145(5).
https://doi.org/10.1061/(ASCE)WR.1943-5452.0001023
Adepu,
S., and Mathur, A. (2016). Distributed Detection of Single-Stage Multipoint Cyber Attacks in a
Water Treatment Plant. In Proceedings of the ACM Asia Conference on Computer
and Communications Security. https://doi.org/10.1145/2897845.2897855
Ahmad,
T., Al-Shaikhli, B., and Al-Kahtani, M. A. (2017). Hybrid
Intrusion Detection System Using
Machine Learning Techniques. International Journal of Computer Applications,
160(7), 1–6.
Axelsson,
S. (2000).
Intrusion Detection Systems:
A Survey and Taxonomy (Technical
Report). Chalmers University.
Cintuglu,
M. H., Mohammed, O. A., Akkaya, K., and Uluagac, A. S. (2017). A Survey on Smart Grid
Cyber-Physical System Testbeds. IEEE Communications Surveys and Tutorials,
19(1), 446–464. https://doi.org/10.1109/COMST.2016.2627399
Conti,
M., Dehghantanha, A., Franke, K., and Watson, S. (2018). Internet of Things Security and
Forensics: Challenges and Opportunities. Future Generation Computer Systems,
78, 544–546. https://doi.org/10.1016/j.future.2017.07.060
Da
Xu, L., He, W., and Li, S. (2014). Internet of Things in Industries: A Survey. IEEE Transactions on
Industrial Informatics, 10(4), 2233–2243.
https://doi.org/10.1109/TII.2014.2300753
Ferrag,
M. A., Maglaras, L., Janicke, H., Jiang, J., and Shu, S. (2020). Deep Learning for Cyber Security
Intrusion Detection: Approaches, Datasets, and Comparative Study. Journal of
Information Security and Applications, 50.
https://doi.org/10.1016/j.jisa.2019.102419
Goh,
J., Adepu, S., and Mathur, A. (2016). A Dataset to Support Research in the Design
of Secure Water Treatment Systems. In Proceedings of the International
Conference on Critical Information Infrastructures Security.
https://doi.org/10.1007/978-3-319-71368-7_8
He,
H., and Yan, J. (2016). Cyber-Physical Attacks and Defenses in the Smart Grid: A Survey. IET
Cyber-Physical Systems: Theory and Applications, 1(1), 13–27.
https://doi.org/10.1049/iet-cps.2016.0019
Hinton,
G. E., Deng, L., Yu, D., Dahl, G. E., Mohamed, A. R., Jaitly, N., Senior, A.,
Vanhoucke, V., Nguyen, P., Sainath, T. N., and Kingsbury, B. (2012). Deep Neural Networks for Acoustic
Modeling in Speech Recognition. IEEE Signal Processing Magazine, 29(6), 82–97.
https://doi.org/10.1109/MSP.2012.2205597
Javaid,
A., Niyaz, Q., Sun, W., and Alam, M. (2016). A Deep Learning Approach for Network
Intrusion Detection System. In Proceedings of the 9th EAI International
Conference on Bio-inspired Information and Communications Technologies.
https://doi.org/10.4108/eai.3-12-2015.2262516
Jin,
P. H., Park, Y. J., and Kim, S. H. (2020). Anomaly Detection in Cyber-Physical Systems
Using Deep Learning. IEEE Access, 8, 102161–102173.
Kim,
Y., Kim, H., and Kim, K. H. (2019). A Deep Learning-Based Intrusion Detection
Framework for CPS. IEEE Access, 7, 103492–103504.
Lee,
E. A. (2008).
Cyber Physical Systems: Design Challenges. In
Proceedings of the 11th IEEE International Symposium on Object-Oriented
Real-Time Distributed Computing (ISORC). https://doi.org/10.1109/ISORC.2008.25
Liu,
X., Li, Z., and Li, C. (2012). Cyber Security and Privacy Issues in Smart Grids. IEEE Communications
Surveys and Tutorials, 14(4), 981–997.
https://doi.org/10.1109/SURV.2011.122111.00145
Mitchell,
R., and Chen, I. R. (2014). A Survey of Intrusion Detection Techniques for Cyber-Physical
Systems. ACM Computing Surveys, 46(4), 1–29. https://doi.org/10.1145/2542049
Mo,
Y., and Sinopoli, B. (2010). False Data Injection Attacks in Control Systems. In Proceedings of the
First Workshop on Secure Control Systems.
Moustafa,
N., and Slay, J. (2015). UNSW-NB15: A Comprehensive Data Set for
Network Intrusion Detection Systems. In Military Communications and Information
Systems Conference (MilCIS). https://doi.org/10.1109/MilCIS.2015.7348942
Munir,
K., Hussain, S. A., and Shah, S. A. (2019). Cyber Attack Detection
in Industrial Control Systems
Using Machine Learning. IEEE Access, 7,
108602–108615.
Pan,
S., Morris, T., and Adhikari, U. (2015). Developing a Hybrid Intrusion Detection
System Using Data Mining for Power Systems. IEEE Transactions on Smart Grid,
6(6), 3104–3113. https://doi.org/10.1109/TSG.2015.2409775
Pasqualetti, F., Dörfler, F., and Bullo, F. (2013). Attack Detection and Identification
in Cyber-Physical Systems. IEEE Transactions on Automatic Control, 58(11),
2715–2729. https://doi.org/10.1109/TAC.2013.2266831
Teixeira,
A., Pérez, D., Sandberg, H., and Johansson, K. H. (2012). Attack Models and Scenarios for
Networked Control Systems. In Proceedings of the 1st International Conference
on High Confidence Networked Systems. https://doi.org/10.1145/2185505.2185515
Wang,
S., Hong, Y., and Chen, J. (2018). Machine Learning-Based Intrusion Detection
for Smart Grid Systems.
IEEE Transactions on Smart Grid, 9(5), 5134–5143.
Zhang, J., Qin, Z., Yin, H., Ou, L., and Li, K. (2008). A Feature Selection Method for Intrusion Detection Systems Based on Support Vector Machine. In Proceedings of the IEEE International Conference on Information and Automation.
|
|
 This work is licensed under a: Creative Commons Attribution 4.0 International License
This work is licensed under a: Creative Commons Attribution 4.0 International License
© IJETMR 2014-2026. All Rights Reserved.