ShodhKosh: Journal of Visual and Performing ArtsISSN (Online): 2582-7472
|
|
IMAGE BASED MERN STACK FOR SERVICE DISCOVERY USING METHOD WEB SERVICE
Dr. Sudhir Kadam 1![]()
![]() ,
Aparna Patil 2
,
Aparna Patil 2![]()
![]() ,
Dr. Sachin Gurav 3
,
Dr. Sachin Gurav 3![]()
![]() ,
Dr. Yogesh Mali 4
,
Dr. Yogesh Mali 4![]()
![]() ,
Dr. Sarang Maruti Patil 5
,
Dr. Sarang Maruti Patil 5![]()
![]() ,
Rajendra More 6
,
Rajendra More 6![]()
![]()
1 School of Engineering, Ajeenkya D Y Patil University, D Y Patil
Knowledge City, Pune, Maharashtra, India
2 Assistant
Professor, Department of ECE, Bharati Vidyapeeth (Deemed to be University)
College of Engineering, Pune, India
3 Associate Professor, Department of E&TC, Sharad Institute of
Technology, Kolhapur, Maharashtra, India
4 School of Engineering, Ajeenkya D Y Patil University, D Y Patil
Knowledge City, Pune, Maharashtra, India
5 Associate Professor, Department of Computer Science and Engineering, Amity School of Engineering and Technology, Amity University Mumbai, Maharashtra, India
6 Assistant Professor, Padmabhooshan Vasantraodada Patil Institute of Technology (PVPIT), Budhgaon, Sangli, India
|
|
ABSTRACT |
||
|
The primary
technologies used to build this "E-commerce web service using MERN"
are Mongodb, Nodejs, Express, and React. All consumers can browse a large
selection of products, but to add a product to their shopping basket, they
must first register and log in. Customers can read reviews made by other
users before making a purchase. The number of items a customer adds to their
shopping basket is up to them. The quantity of a product put on the cart can
thereafter be modified by the customers. Finally, customers can enter their
information during checkout and submit their order by paying the appropriate
amount for it. The administrator can then view the customer's data, including
order details, the delivery address for the order, and whether the payment
has been received. Due to the inability to try on clothing while purchasing
clothing online, it might be challenging for a consumer to choose a desirable
outfit on the first try. The virtual try-on assignment has the potential to
greatly increase the effectiveness of creating fashion catalogues and improve
online user experience. This undertaking seeks to address this issue. |
|||
|
Received 11 December 2025 Accepted 09 March 2026 Published 28 March 2026 Corresponding Author Aparna
Patil, aspatil1@bvucoep.edu.in DOI 10.29121/shodhkosh.v7.i2s.2026.7038 Funding: This research
received no specific grant from any funding agency in the public, commercial,
or not-for-profit sectors. Copyright: © 2026 The
Author(s). This work is licensed under a Creative Commons
Attribution 4.0 International License. With the
license CC-BY, authors retain the copyright, allowing anyone to download,
reuse, re-print, modify, distribute, and/or copy their contribution. The work
must be properly attributed to its author.
|
|||
|
Keywords: E-Commerce, Logic Search, Machine Learning, Web
Discovery |
|||
1. INTRODUCTION
Through this concept, customers will be able to shop virtually online and buy the things of their choice from the vendor. Web-based purchasing is the process by which customers buy goods from a seller gradually over the Internet without the need for a middleman. It's a particular form of electronic trade. This initiative explains the advantages of online shopping to customers of a physical store Chanana and Goele (2022), Fortune (2016). Using a website and the internet, it enables you to purchase items from a store from anywhere in the globe. So, the customer will be able to shop online and have their selected seller deliver their items to their home. As opposed to other websites already in existence, this research work has goals that would address a present issue in the realm of online buying Zhang et al. (2019), Zhang et al. (2017).
The two main groups in this research work are the Administrator and the Users. The store manager acts as the administrator. Administrators have the ability to add, edit, update, or remove products. This includes changing product names, prices, and adding or removing products, among other things Cao et al. (2017), VITON (2018).
The User's sole options at the online store are to browse and add products to their cart. Only the shop may be used by the user. Eight chapters make up this thesis, which explains the research effort Lee et al. (2022), Gong et al. (2022). The defines technologies and tools used; and describes the application and procedure presents the MVC layout; describes the database and GUI designs; implementation process Kadam and Chavan (2019), Cassar et al. (2011).
2. RELATED WORK
The notion of online shopping is discovered by a careful analysis of prior relevant studies pertain-ing to the many concepts of online shopping. This is known as a literature review. It covers the cur-rent state of online shopping, its significance, problems, and variables that influence it, as well as a critical analysis of the privacy and security concerns associated with it.
Consumers virtually equally weigh the cost of the product and the cost of shipping when comparing one purchase to another. There are a few things that merchants may do to enhance the online shopping experience for their customers. Customers are willing to wait for their goods, but they want to know exactly how long that wait will be. The first thing to write down is the projected delivery date of the item. Customers are encouraged to endorse an online retailer by the promptness of goods deliveries. Customers also want delivery notifications and tracking information to know when their packages will arrive. Online buyers prefer shipping options that are flexible, particularly those that allow them to specify special delivery instructions or set a certain time for de-livery. Customers desire the option of amending their address if they enter it incorrectly while making purchases online.
3. PROBLEMS IN EXISTING SYSTEM:
3.1. Financial Frauds
Since the first online businesses started popping up on the internet, financial fraudsters have been a concern for enterprises. Financial fraud comes in many different forms and is widespread in the e-commerce industry.
3.2. Poor fit
One of the main issues for e-commerce firms that results in them suffering significant losses is returns brought on by poor fit. It is disappointing for the client as well to re-turn garments that don't fit after a few days of waiting.
3.3. Security Threats
Security has always been the main issue for the e-commerce industry. Despite having a successful marketing strategy and a top-notch website design, the entire website and your company could be quickly destroyed by a straightforward DDoS attack or other cyber threats.
4. IMPLEMENTATION
In academic research, scientific experimentation, corporate analysis, and other domains where a methodical and rigorous approach is required to obtain trustworthy results, the methodology is frequently employed. Model, View, and Controller are the three parts of the Model-View-Controller (MVC) architecture used by MERN. Model: controls the application domain's behavior and data.
Figure 1
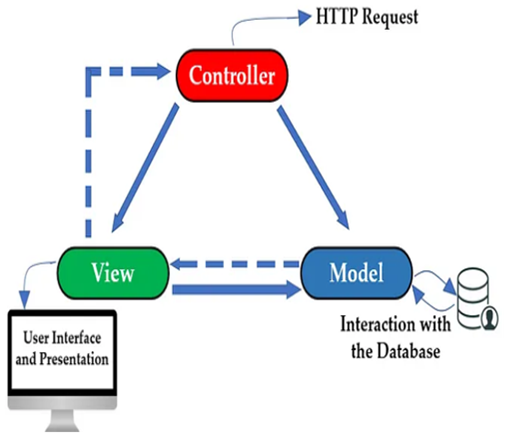
Figure 1 Architecture of Application Using Web Service Discovery
View: creates a user interface element that renders the model into a form appropriate for interaction.
Controller: accepts user input and calls on model objects to start a response.
MVC and MERN
Due to its support for both the server and the browser, MERN is not an MVC framework in the conventional sense. Another option to implement MVC is to stick with server-side tinplating in Node, simply transmit HTML to the browser, and consider the browser as the View layer. This is known as doing things the old-fashioned way. However, MVC is used when React is paired with a java script backend. React is the "V" in the MVC model. Mongoose models define the data component. All the necessary data that our program needs to function will be retained here. All functional programming is done via Express and Node.js, and these two frameworks will be used to write the Business Logic Tier (controller). This layer represents the application server that will act as a communication channel between the client and database. This layer will accept user HTTP requests, send React components to the user's device, and react appropriately. React represents the "V" in the MVC. Our client tier (View), which will be based on the ReactJS framework, will be created using JavaScript, HTML, and CSS. In order to access our application's functionality, the user will interact with this level of the architecture.
4.1. Design Tools Used
This report aims at exploring the effects of Virtual Try-On in the e-commerce environment and giving an in-depth insight into the advantages and disadvantages of this technology. The report will be set as follows:
4.2. Technology and Implementation.
In this section, a detailed description of the technologies that Virtual Try-On is based on, including AR and VR, will be presented. It will discuss how these technologies are implemented into e-commerce solutions and what technical factors should be considered when adopting Virtual Try-On solutions.
4.3. Benefits and Challenges
In this case, the report is going to talk about the many advantages that go hand in hand with the Virtual Try-On in e-commerce which includes improved customer experience, more confidence in decisions made in purchasing the product and decreased returns. Also, the paper will discuss the hurdles the businesses can face when using Virtual Try-On, including technological constraints, user acceptance, and the necessity to have quality product renderings.
4.4. Case Studies
This part will present real-life examples of successful Virtual Try-On applications in the e-commerce sector. Future Trends and Opportunities: The report will discuss future opportunity of Virtual Try-On in e-commerce. It will refer to the emerging trends, technology development, and possible growth areas. Also, it will explore how consumer expectations continue to change and how Virtual Try-On can assist in satisfying them.
4.5. Conclusion and Recommendations
The report will be a summary of the main findings and observations of the study. It will give practical suggestions to e-commerce companies that want to apply Virtual Try-On, such as best practices, ways of maximizing the value, and ideas on how to overcome the difficulties.
The objective of this report is to delve into the impact of Virtual Try-On in the e-commerce industry and provide a comprehensive understanding of its benefits and limitations. The report will be structured as follows:
5. Definition and Significance of Background Image Removal
Background image removal or image segmentation or background subtraction refers to the creation of background removal on a double of isolating the foreground objects or subjects. It is of great importance to numerous applications, which include image editing, object recognition, computer vision, and e-commerce. The background is precisely removed to place the emphasis on the foreground objects and this allows the images to be analyzed, manipulated, or integrated easily into other contexts.
Background image removal is also important since it has the capability of removing the main subjects of images, enabling them to be flawlessly fitted into various backgrounds or they can be fused together with other images. It offers image editing opportunities to change flexibility, increase the visual quality, and allow designing interesting visuals in marketing, advertising, and multimedia presentation.
6. Techniques and Algorithms for Background Removal
Background image removal has a number of techniques and algorithms that are used depending on the complexity and accuracy required. Among the methods that are in common use are:
6.1. Color based Methods
Such techniques are based on the color value of pixels to identify the foreground and background. The foreground is segmented (or partitioned according to color difference) by techniques like chroma keying (a single color is used as reference) and color thresholding (a range of colors is defined).
6.2. Edge Detection Methods
The edge detection algorithms, including the Canny edge detector, are aimed at detecting the sudden shifts in pixel intensity in order to find object boundaries. The foreground could be discriminated on the basis of edge in-formation by the detection of edges between the foreground and the background.
The graph cut and Grab Cut, make use of the principles of graph theory in order to model the image as a graph and optimize the fore-ground-background segmentation. These techniques normally involve user input, e.g. defining initial foreground and background areas, or giving approximate segmentation sketches.
7. Implementation Steps and Challenges
Background image removal entails a number of steps as they include:
7.1. Pre-processing
color space conversion and contrast enhancement with the aim of enhancing the superiority and precision of algorithms at removing back-grounds in Figure 2 and Figure 3.
7.2. Foreground/Background Separation
Depending on the technique or algorithm used, the image is acted on to separate the foreground and the conditions. This might include thresholding, edge detection, machine learning-based segmentation or graph-based optimization as shown in Figure 4 and Figure 5.
7.3. Refinement and Post-processing
In order to enhance the quality of the segmentation, the post-processing such as morphological processing, smoothing, and region filling can be used to enhance the obtained foreground and eliminate artifacts or flaws in Figure 6 and Figure 7.
7.4. Integration or Application
After background has been cleared, the extracted foreground may be easily incorporated into a new background or even mixed with other images as that which may be needed in the particular task or application.
8. Challenges in background image removal include
8.1. Complex Backgrounds
Complex or disordered backgrounds of images can be difficult to properly segment, and may need more sophisticated algorithms or human intervention.
8.2. Background/object Occlusion
As the foreground objects are spreading and obscuring each other, it is more difficult to correctly distinguish the objects in the foreground and the ones in the background, which demands advanced algorithms that would be able to deal with the concept of occlusion.
8.3. Clearness and Reflections
The interaction of light with the transparent or reflective objects may make it hard to isolate them against a background, specific algorithms are required to address such situations.
8.4. Real-time Processing
Background removal algorithms have limits on time such as real-time applications like video processing, which need to be implemented efficiently and fast to keep the operation running smoothly.
Qualitative analysis implies the analysis of the results by visual tools to evaluate the quality of the segmentation, such as the detail that is retained, the smoothness of object edges and the lack of artifacts and residual background. Subjective scores and user feedback can be useful in the analysis of perceptual quality of removed background.
9. Implementation Workflow and Considerations
The general steps of the implementation process of Open Pose coordinate extraction are as follows:
9.1. Preparation
Install the hardware and software dependencies, such as compatible GPUs to perform computations effectively as well as installing the open pose libraries and dependencies.
9.2. Input Acquisition
The input images or videos in which the body key point should be obtained must be acquired. Make sure the input is of quality and resolution to detect the key points.
9.3. Open Pose Configuration
Tune Open Pose parameters, including the model architecture, input resolution, key point confidence threshold, and other applicable parameters depending on the needs of the application.
9.4. Key point Extraction
Use Open Pose to process the input videos or images to get the 2D position of the body key points. The result may be in the form of JSON, CSV, and other structured formats.
9.5. Post-processing
Take any desired post-processing to the extracted key points like filtering, interpolation or smoothing to improve the accuracy and consistency of the coordinates.
9.6. Normalization and Encoding
The obtained annotated data is normally put to a normal state and encoded to an appropriate format to be trained by Dense Pose algorithm. This can include pixel-level correspondences, body part names, or some other useful metadata.
Factors to be looked into during implementation would be hardware resources since Open Pose can be computationally expensive and the architecture to use the Open Pose model will differ depending on the preference between accuracy and speed.
9.7. Virtual Try-On System Integration
The process of open Pose coordination extraction can be incorporated into a virtual try-on system in order to allow real-time pose estimation and fitting of garment. The virtual try-on system can be used to provide real-time simulations of how a garment would look on the body of the user by superimposing the extracted body key points with the 3D garment models.
The integration process includes matching the extracted key points and the relevant vertices (joints) of the 3D model of the garment, transforming and deforming the garment, and visualizing the virtual try-on outcome.
9.8. Performance Evaluation and Benchmarking
To assess the effectiveness of Open Pose coordinate extraction, one may refer to such content parameters as key point detection accuracy, tracking stability and computational efficiency. Also, one can use benchmark datasets that contain ground truth annotations to compare the performance of various Open Pose configurations or models.
The qualitative assessment is based on the visual analysis of the main points extracted and monitoring of quality to determine the accuracy and consistency. The field testing under various human poses and environmental conditions can give a useful amount of information on the robustness and reliability of the system.
Figure 2
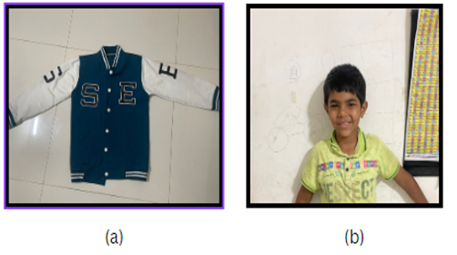
Figure 2 Pre-Processing
Figure 3
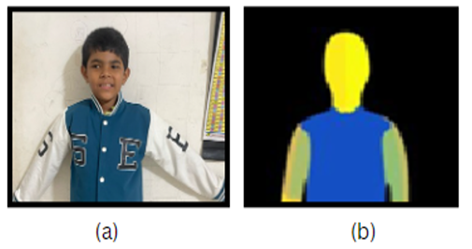
Figure 3 Foreground/Background
Figure 4
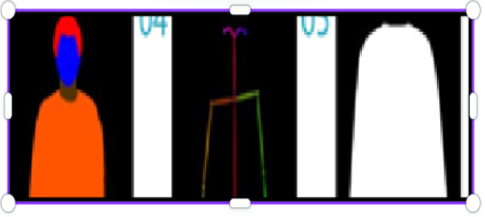
Figure 4 Foreground/Background Separation and Occlusion
Figure 5

Figure 5 Real-Time Processing Transparency and Reflections
Figure 6
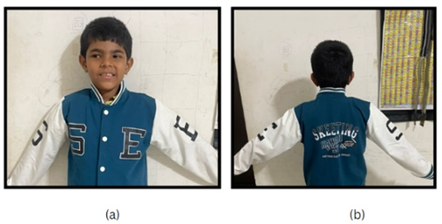
Figure 6 Out Put Image
10. Evaluation and Future Enhancements
Cloth segmentation algorithms can be assessed based on such measurements as F1 score, pixel accuracy, precision, recall, and intersection over union (IOU). Better Robustness: Learn to produce algorithms with better capacity to deal with complex clothing patterns, occlusions, transparency and various lighting conditions.
1) Real time Performance- cloth segmentation algorithms in real time or near real time to enable interactive virtual try-on.
2) Dataset Expansion- Training segmentation models on a broad variety of clothes and poses by building larger and more varied datasets that are annotated.
3) Multimodal Approaches- Adding other sources of information, including depth sensors or multi-view cameras to make cloth segmentation more accurate and robust.
11. Conclusion
The combination of a good try-on experience into an online shopping platform has many benefits to the customers and the businesses. Virtual try-on addresses the shortcomings of conventional Internet based shopping in that no-one can physically attempt on clothes; this makes it a better shopping experience and overcomes the barrier between offline and online shopping. The customers will have the advantages of convenience of online shopping and are able to see how the products fit, their style and appearance on their own bodies.
In the case of businesses, virtual try-on can result into more customer satisfaction, less returns, and brand loyalty. It creates the possibility of personalized and interactive customer interaction, which will eventually lead to sales and revenue increase. Moreover, the virtual try-on technology is a cutting-edge innovation that places the businesses at the pinnacle of competition compared to their rivals in the competitive e-commerce sector.
Nevertheless, its implementation has to be done carefully focusing on aspects of user experience, security, performance, and integration with the current e-commerce platforms. The virtual try-on technology requires constant research and development to be refined, more accurate, and more products can be virtually tried on.
To sum it up, the application of virtual try-on in an online store can transform online shopping of apparel and accessories. Through the utilization of this technology, companies are able to improve the customer experience, increase sales, and position themselves as a leader in the emerging world of e-commerce.
CONFLICT OF INTERESTS
None.
ACKNOWLEDGMENTS
None.
REFERENCES
Cao, Z., Simon, T., Wei, S.-E., and Sheikh, Y. (2017). Realtime Multi-Person 2D Pose Estimation. Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition.
Cassar, G., Barnaghi, P., and Moessner, K. (2011, August). A Probabilistic Latent Factor Approach to Service Ranking. 2011 IEEE International Conference on Intelligent Computer Communication and Processing (ICCP) (103–109). IEEE. https://doi.org/10.1109/ICCP.2011.6047850
Chanana, N., and Goele, S.
(2022). Future of E-Commerce in India.
International Journal of Computing and Business Research, Proceedings of
I-Society (2022).
Fortune. (2016). Consumers are Now Doing Most of Their Shopping Online. Fortune.
Gong, K., Gao, Y., Liang, X., Shen, X., Wang, M., and Lin, L. (2022). Graphonomy: Universal Human Parsing Via Graph Transfer Learning. Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition.
Guo, W.-Y., Quhai-Cheng, and Chen, H. (2010). Semantic Web Service Discovery Algorithm and Its Application on the Intelligent Automotive Manufacturing System. 2010 International Conference on Information Management and Engineering. IEEE. https://doi.org/10.1109/ICIME.2010.5478166
Kadam, S. A., and Chavan, M. S. (2019). Design of Digital Filter by Differential Evolution. International Journal of Recent Technology and Engineering, 8(2), 2207–2210. https://doi.org/10.35940/ijrte.B2420.078219
Kadam, S., Kadam, P., Jadhav, P., Gurav, S., Patil, V., and Prabhakar, A. (2024). Atmospheric Water Generator Using Smart Automation Systems. SSRG International Journal of Electrical and Electronics Engineering, 11(4), 206–216. https://doi.org/10.14445/23488379/IJEEE-V11I4P122
Kadam, S., and Chavan, M. S. (2019). Design of Digital Filter by Differential Evolution. International Journal of Recent Technology and Engineering, 8(2), 2207–2210. https://doi.org/10.35940/ijrte.B2420.078219
Kadam, S., and Chavan, M. S. (2019). Design of Digital Filter by Genetic Algorithm. International Journal of Engineering and Advanced Technology, 8(6), 397–400. https://doi.org/10.35940/ijeat.E7808.088619
Kadam, S., and Chavan, M. S. (2019). Design of Digital Filter by Genetic Algorithm. International Journal of Engineering and Advanced Technology, 8(6), 397–400. https://doi.org/10.35940/ijeat.E7808.088619
Lee, S., Gu, G., Park, S., Choi, S.,
and Choo, J. (2022). High-Resolution Virtual Try-on
with Misalignment and Occlusion-Handled Conditions. Proceedings of the IEEE
Conference on Computer Vision and Pattern Recognition.
Ma, J., Cao, J., and Zhang, Y. (2007, May 8–12). A Probabilistic Semantic Approach for Discovering Web Services. Proceedings of the 16th International Conference on World Wide Web (WWW 2007). ACM.
Rajendran, T., and Balasubramanie, P. (2010). An Optimal Agent-Based Architecture for Dynamic Web Service Discovery With QoS. 2010 Second International Conference on Computing, Communication and Networking Technologies. IEEE. https://doi.org/10.1109/ICCCNT.2010.5591673
VITON. (2018). An Image-Based Virtual Try-on Network. Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition.
Wei, W., Barnaghi, P., and Bargiela, A. (2010). Probabilistic Topic Models for Learning Terminological Ontologies. IEEE Transactions on Knowledge and Data Engineering, 22(7), 1028–1040. https://doi.org/10.1109/TKDE.2009.122
Wengerong, and Liu, K. (2010). A Survey of Context-Aware Web Service Discovery: From User's Perspective. 2010 Fifth IEEE International Symposium on Service Oriented System Engineering. IEEE. https://doi.org/10.1109/SOSE.2010.54
Zhang, T., Cao, L., and Wang, W. Y. C. (2017). The Impact of Virtual Try-On Image Interaction Technology on Online Shoppers' Purchase Decision. Proceedings of the 2017 CHI Conference Extended Abstracts on Human Factors in Computing Systems. https://doi.org/10.1145/3026480.3026484
Zhang, T., Wang, W., Cao, L., and Wang, Y. (2019). The Role of Virtual Try-On Technology in Online Purchase Decisions from Consumers' Aspect. Internet Research. https://doi.org/10.1108/IntR-12-2017-0540
Zhou, B., Tingleihuan, J., and Shen, M. (2009). Using Inverted Indexing to Semantic Web Service Discovery Search Model. 2009 5th International Conference on Wireless Communications, Networking and Mobile Computing. IEEE. https://doi.org/10.1109/WICOM.2009.5301035
|
|
 This work is licensed under a: Creative Commons Attribution 4.0 International License
This work is licensed under a: Creative Commons Attribution 4.0 International License
© ShodhKosh 2026. All Rights Reserved.

